Security: Target: Linux Network Devices Abstract:
Widespread use of Microsoft operating systems on the desktop and server have been increasingly exploited by malware for dubious uses. The ever growing increased use of Linux on low-end network devices have made an interesting target for malware creators. Most recently, attacks using compromised Microsoft platforms have been targeting low-end Linux network devices.
History:
Malware, which cooperates with one another over the internet have been called Botnets. They have taken over Microsoft PC's and Servers, because of their ubiquitousness, across the globe. They can be very difficult to find and destroyed, as demonstrated by the Kneber botnet. First known activity for Kneber dates back to March 2009.
As the popularity of Linux grew, the movement of malware from Microsoft platforms to Linux platforms began
In January 2008, a DNS attack on DSL modems was discovered in Mexico. The 2Wire DSL modems were targeted, re-directing people from a Mexico bank to a site falsely demonstrating itself to be a bank.
In January 2009, the Psyb0t was discovered, targeting MIPS based Linux devices.
In February 2010, the Chuck Norris Botnet targeted D-Link Linux based devices.
Sometimes, the network devices are merely used to perform distributed denial of service attacks against corporations or entire nations, as what is happening in South Korea during March 2011.
These botnets are dangerous and could be used to infiltrate other devices on a network, which are then used to gather information, for the purpose of theft or other illegal nefarious behavior.
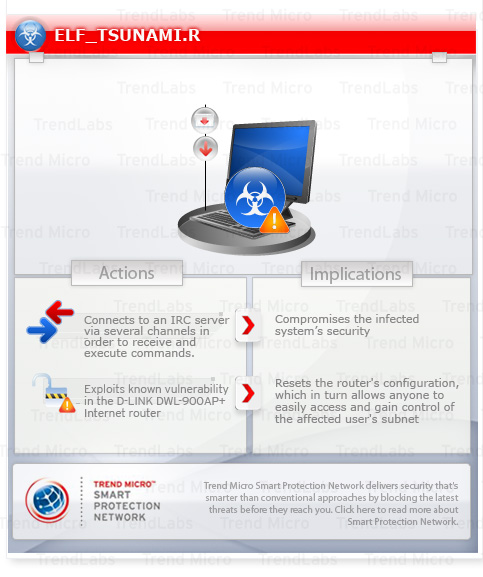
Enter: Elf_Tsunami.R
In March 2010, a new exploit has been discovered. Elf_Tsunami.R was uncovered by TrandLab. The D-Link DWL-900AP+ is vulnerable, as well as other devices. Formerly exploited Microsoft systems infected with malware can attack and infiltrate the Linux network devices on the local area network.
Elf_Tsunami.R leverages Internet Relay Check (IRC) servers as an independent transport, after the Linux network device is infiltrated, meaning PC anti-virus software can not completely clean out your network, after cleaning your PC.
Network Management Connection:
It has long been expected that Linux would remain more secure to attacks, over Microsoft based appliances, desktops, and servers. Linux consumer based devices, however, are widely available and do not necessarily meet the stringent security requirements for Enterprise and Managed Services networking infrastructure.
Caution should be taken when employing Microsoft and Linux platforms in an Enterprise and Managed Services networking infrastructure, because of the increased use of hybrid exploits. The possibility of infecting customer networks through their implementation is not out of the question, as demonstrated by millions of globally exploited systems and devices.
No comments:
Post a Comment